Seeing 2025, businesses are facing more complex cyber threats in 2026 than ever… because attackers are now using AI to scan for and exploit vulnerabilities at record speed, and even reports say that. IBM reported that there was a 44% jump in attacks via known application vulnerabilities in 2025, fueled by AI-driven scanning tools. Attacks using ransomware have also increased by 49% compared to 2024, while supply chain attacks have increased nearly fourfold since 2020.
So, in short, every company regardless of size is now a target for cyber-attacks. A report by NordLayer found that in 2022, 43% of all ransomware and data breaches targeted small and medium-sized companies while 60% of those small businesses targeted by cybercriminals went out of business within 6 months of the incident.
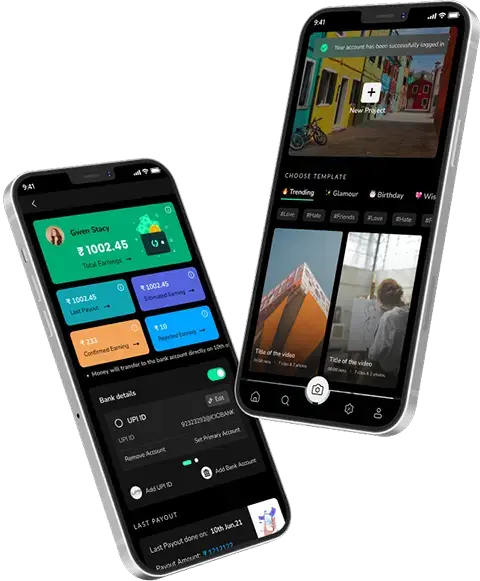
Furthermore, your work model has changed which has introduced new risks. More businesses are working remotely, utilizing cloud-based systems to conduct business, and using mobile applications to connect employees and customers. This has improved efficiency of course but has also increased exposure, for example, when a business relies on solutions built by a mobile app development company, it becomes important to make sure that those applications are secure because even a small gap can be exploited.
So, the focus is not just on having tools, but on following the best cybersecurity practices for businesses, and making sure everything is aligned. You need proper network security measures for companies, and also strong data protection strategies for businesses because data is what attackers are really after. And if you are thinking how to protect business from cyber attacks, then you must build a layered and updated approach.
In short, cybersecurity measures for businesses in 2026 must be holistic and up-to-date. We’ve shared 10 measures below that are ranked by priority and impact.
These are not overly technical ideas, but clear and useful cybersecurity tips for small businesses, and even larger ones, so that you are better prepared and not caught off guard in 2026.
So let’s get started.
Top 10 Cybersecurity Measures For Businesses to Prevent Cyber Attacks in 2026
| Cybersecurity Measures | Priority | Cost | Complexity | Impact |
| 1. Identity & Access Management | High | Medium | Medium | High |
| 2. Data Encryption & Protection | High | Medium | Medium | High |
| 3. Patch & Vulnerability Management | High | Low/Med | Medium | High |
| 4. Endpoint & App Security | High | Medium | Medium | High |
| 5. Network & Remote Security | Medium | Medium | High | Medium |
| 6. Monitoring & Incident Response | High | High | High | High |
| 7. Backups & Disaster Recovery | High | Medium | Low | High |
| 8. Security Training & Awareness | Medium | Low | Low | Medium |
| 9. Third-Party Risk Management | Medium | Low | Medium | Medium |
| 10. Governance & Compliance | Medium | High | High | Medium |
1. Identity & Access Management (IAM)
Controlling who can access your systems is one of the most basic and most important steps. Because most cyber attacks actually start with weak or stolen passwords. So if access is not managed properly, it becomes an easy entry point.
You should enable Multi-Factor Authentication (MFA) wherever possible, this way, users don’t just rely on passwords but they can also use things like one-time codes, biometrics, or hardware tokens. It’s especially important for admin accounts and external logins, because they carry higher risk.
At the same time, businesses are now moving towards a Zero Trust approach. This simply means you don’t trust any login automatically even if it’s coming from inside your network. Every access request is verified.
Also, make sure your password policies are strong. Passwords should be long, unique, and not reused. Using a central password manager helps here, especially for teams. Along with that, Role-Based Access Control (RBAC) should be applied, so that users only get access to what they actually need. Nothing extra.
And yes, regular audits are important too… because over time, unused accounts and unnecessary admin access start piling up, and that creates risk.
These steps together form one of the most important cybersecurity measures for businesses and they are often considered among the best cybersecurity practices for businesses today.
- Implementation: You can use identity management tools (Azure AD, Okta, or Google Workspace) based on your setup. MFA can be set using Duo, Auth0, or Microsoft Authenticator tools in emails, VPNs, and servers as well. It’s also a good way to review access regularly and to remove outdated accounts.
- Effort/Cost: Medium. The tools themselves are usually affordable, especially for SMBs but setting up a complete IAM or Zero Trust system can take time and effort.
- KPIs
- % of users using MFA
- number of privileged (admin) accounts
- time taken to revoke access
- reduction in phishing-related breaches
2. Data Encryption & Protection Strategies
Protecting your business data is important as well as necessary because even if attackers somehow get into your systems, strong encryption makes sure they cannot actually read or use the data.
So the first step is to understand your data; you must first identify the data that requires protection. You need to understand your company’s customer records, employee records, financial records, and intellectual property.
Whenever possible, implement encryption for your data in both stored format and during transit – a strong encryption standard like AES should be used for stored data, and for data in transit, you should use secure communication protocols such as SSL, TLS, or VPNs to help protect your data from interception while being transmitted over the Internet.
You should also implement DLP tools to monitor the movement of sensitive data through your organization and prevent unauthorized sharing of that data. DLP implements another control point for sensitive data.
Finally, you should limit the amount of sensitive data that is exposed to your organization’s network. You can limit access by creating network segmentation. This way, you can keep servers that are containing sensitive data, separate from other servers within your organization’s network. This will help limit exposure to damage in the event that computers connected to your network are compromised by hackers. Tokenization and the use of secure vaults are examples of preventing exposure of sensitive data to your organization’s network.
All of this together forms a strong base for data protection strategies for businesses, and is also a key part of the cybersecurity measures for businesses that companies should not ignore.
- Implementation: Set encryption on disks and databases. Also use built-in cloud tools like AWS KMS or Azure Key Vault. Just make sure that all web services and VPNs are secured with TLS. DLP tools can be installed across emails, endpoints, and cloud storage, and yes, set up proper access control and network segmentation with the help of VLANs or subnets to isolate critical data.
- Effort/Cost: Medium. Encryption tools may have licensing cost, and key management requires discipline (rotate keys, back-ups). Network segmentation can be a higher effort.
- KPIs
- % of sensitive data encrypted
- incidents of unauthorized data exfiltration
- volume of data stored in backups
- results from data leak or exfiltration tests
3. Patch & Vulnerability Management
Unpatched software is one of the easiest ways for attackers to get in and it happens more often than you’d think… because updates are delayed, or sometimes ignored. Reports have shown that a large number of cyberattacks actually happen due to known vulnerabilities which already had fixes available but they were not applied in time.
So, the idea is simple. Keep everything updated, and do it regularly.
Start by creating an inventory of all your systems like servers, laptops, network devices, even IoT devices if you use them because if you don’t know what you have, you cannot protect it properly. Once that’s done, make sure critical patches are applied quickly, without unnecessary delays.
You should also automate updates wherever possible. Tools like Windows Update Services, Linux repositories, cloud auto-updates, and mobile device management (MDM) systems can help here. Automation reduces the chances of missing something… and makes the whole process smoother.
Routine vulnerability scans are another very important part of security because they can help you identify vulnerabilities that need to be patched, whether it be an outdated patch or a bad configuration; there are many types of vulnerabilities. Therefore, Nessus and Qualys scanning tools are used for this. And once issues are found, they should be fixed based on priority, that means, critical vulnerabilities first, followed by those with a lower priority.
Also keep an eye on security updates from vendors. Because new threats keep coming and when you stay informed, you can act quickly. For this, you must use alerts from trusted sources.
Also Read – Enhancing Cybersecurity with Generative AI: Transforming Threat Detection & Defense
All of this becomes a key part of network security measures for companies and also supports overall cybersecurity measures for businesses, especially when the goal is clear – how to protect business from cyber attacks before they even happen.
- Implementation: You can use patch management tools like Microsoft WSUS, Automox, or ManageEngine to automate updates. For network devices, centralized management systems from vendors like Cisco or Fortinet can help. Run vulnerability scans regularly (quarterly is a good start), and maintain an updated list of all assets along with a proper patch schedule.
- Effort/Cost: Medium. Many tools are affordable or even free, but time is needed for testing updates and running scans. It can get a bit complex if your environment includes multiple systems or older (legacy) setups.
- KPIs
- % Percentage of systems fully updated
- average time to fix critical vulnerabilities
- number of unpatched high-risk issues
- rate at which scan issues are resolved
4. Endpoint & Application Security (Including Mobile)
Every device and every application connected to your network needs to be protected. Because even one weak endpoint… can open the door for an attack.
Start with the basics. Antivirus and anti-malware tools are still important and they should be installed on all systems like PCs, servers, everything. However, simply having antivirus is no longer sufficient, we now have Advanced tools such as Endpoint Detection and Response (EDR) to identify suspicious activity as well as thwart threats in real-time.
In addition all applications must remain up to date due to the fact that out-of-date applications tend to have known exploits. Attackers target these types of overruns instantly after discovery. In addition, Secure Software Development practices should be adhered to when creating or using Software that you build or utilize. This includes proper Code Reviews, Security Testing, and adherence to established coding standards such as OWASP to eliminate many potential issues that might occur at launch.
With many businesses now leveraging mobility and working remotely, mobile security is critical as well. Smartphones and tablets should have Device Encryption enabled and Screen Locking should be mandatory. MDM (Mobile Device Management) enables central management of these types of policies across an organization.
Security should also be integrated into the design of mobile applications, regardless of whether they are developed internally or have been built by a mobile application development company. Things like secure authentication (OAuth or OIDC), input validation, encrypted storage, and regular testing should be included. Because fixing security later… is always harder.
This approach is part of the best cybersecurity practices for businesses, and also supports overall cybersecurity measures for businesses, especially when dealing with multiple devices and applications.
- Implementation: Install EDR tools on all systems, and make sure auto-updates are enabled for browsers and commonly used software. For mobile devices, set up MDM solutions that enforce encryption and strong passwords. It’s also a good idea to conduct regular application security reviews, or even bring in experts for testing.
- Effort/Cost: Medium to High. Advanced security tools like EDR and enterprise MDM can be expensive, and application security may require trained developers or external audits.
- KPIs
- % endpoints with active EDR agent
- % devices compliant with MDM policies
- number of malware incidents blocked
- vulnerabilities found/fixed in apps.
5. Network Security & Secure Remote Access
Your network is where everything connects… and if it’s not secured properly, it becomes an easy target. So, protecting both the outer layer and the internal network is important.
At the entry level, you should use a next-generation firewall. This helps filter traffic, block unwanted access, and even stop certain types of attacks before they enter. You can set rules like IP restrictions, location-based access, and intrusion prevention so that only trusted traffic gets through.
Inside the network, segmentation is important. This means separating critical systems and sensitive data into different zones because if one part is compromised, the attacker should not be able to move freely everywhere.
Access control also matters a lot. VPN and Wi-Fi access should only be allowed to verified users and devices. Use strong Wi-Fi security (like WPA3), and require authentication methods such as device certificates or multi-factor login.
And with remote work being common now, employees should not access systems through unsecured networks. A secure VPN or zero-trust access system should always be used. Ideally, devices should automatically connect to the company VPN when they are outside the office… so that there are no gaps.
Monitoring is another key part. You need to continuously watch network traffic, because unusual activity often shows early signs of an attack. Tools like IDS and IPS can help detect suspicious patterns. You can also use Network Access Control (NAC) to make sure only approved and secure devices are allowed to connect.
All of this forms a strong base for network security measures for companies, and is also a critical part of overall cybersecurity measures for businesses, especially in a remote and cloud-driven environment.
- Implementation: Set up firewalls and routers with strict access rules. Enable VPN with multi-factor authentication for all remote users. Install IDS/IPS systems and turn on logging across network devices. You can also use monitoring tools or cloud-based services to track activity. And yes, your IT team should regularly review logs… or rely on alert systems if needed.
- Effort/Cost: High. Advanced network security tools and continuous monitoring can be expensive. However, managed services can help reduce the cost and complexity, especially for smaller businesses.
- KPIs
- number of intrusion attempts blocked
- % of devices connected through VPN
- time taken to detect unusual network activity
- network uptime and stability
- coverage of network segmentation
6. Threat Monitoring & Incident Response
Preventing attacks is important, yes… but it’s not always enough. Because no system is 100% secure, and at some point, something can slip through. So, detection and quick response become just as important.
You need to continuously monitor your systems, and that’s where tools like SIEM come in. A SIEM (Security Information and Event Management) system collects data from across your network (endpoints, servers, cloud systems) and then alerts you if something unusual happens. It helps you spot threats early, before they turn into something bigger.
You can also use threat intelligence feeds, which provide information about known attackers and suspicious activities. And when combined with EDR logs or even managed detection services, your visibility improves a lot… which is what you need.
But monitoring alone is not enough. You also need a clear Incident Response (IR) plan. This is basically a step-by-step process of what to do when an attack happens. It should cover everything, from identifying the issue to containing it, fixing it, and then reviewing what went wrong.
A commonly followed approach is the NIST lifecycle, which includes preparation, detection, containment, recovery, and post-incident review. And yes, this plan should not just exist on paper… it should be tested regularly through drills and simulations.
Because when a real alert comes in, your team should act immediately. First confirm the issue, then isolate it, and stop it from spreading. Speed matters a lot here, especially now when attacks are faster and more automated.
This is why threat monitoring is considered one of the best cybersecurity practices for businesses, and a critical part of overall cybersecurity measures for businesses.
- Implementation: You can deploy a SIEM tool or use cloud-based monitoring services. Set up proper logging across systems, and define clear roles for incident handling. Conduct regular security drills, like phishing simulations. You can also use automation tools to respond faster such as isolating infected devices automatically.
- Effort/Cost: Medium to High. Some SIEM tools and managed services can be expensive, but there are open-source options available. The main effort also goes into planning and running regular drills.
- KPIs
- mean time to detect (MTTD) threats
- mean time to respond (MTTR) to incidents
- number of incidents in a given period
- time taken to contain a breach
- performance in security drills
7. Regular Backups & Disaster Recovery
No matter how strong your security is, breaches or system failures can still happen, so having reliable backups is essential because when things go wrong (like ransomware or hardware failures) backups are your safety net.
Make sure backups are done regularly. Ideally, critical systems should be backed up daily, and don’t just keep backups on the same network; store encrypted copies offsite, either in the cloud or on air-gapped storage that’s disconnected from the main network.
Testing backups is just as important as creating them. You need to regularly restore data from backups to make sure they actually work. Also, implement clear data retention policies. Keeping unnecessary sensitive data can increase risk, so only retain what you really need.
Following these practices is part of data protection strategies for businesses, and one of the key cybersecurity measures for businesses to minimize downtime and loss.
- Implementation: Use automated backup tools like Veeam, Acronis, CrashPlan, or cloud backup services. Organize systems by importance, and back up critical ones more frequently. Follow the 3-2-1 rule: 3 copies of your data, 2 different types of media, and 1 copy offsite. Document recovery steps and run tests at least quarterly.
- Effort/Cost: Medium. Medium. Cloud backups are often affordable, but storage costs increase with larger datasets. Regular testing adds some overhead, but it’s worth it.
- KPIs
- backup success rate
- recovery Time Objective (RTO) achieved in drills
- data recovery integrity (verification of restored data)
8. Security Awareness Training & Culture
Even with the best technology, humans are often the weakest link. Mistakes like clicking on phishing emails or mishandling data can cause big problems, that’s why regular security training is essential.
Train all employees on things like phishing, safe browsing, password hygiene, and proper data handling. Practical exercises work best, for example – sending fake phishing emails to see who clicks and then training them on what went wrong. NIST even calls a security-aware workforce “one of the most effective defenses.”
It’s also about culture. Make security everyone’s responsibility. Share bite-sized tips, celebrate staff who report suspicious emails and make sure people know that their actions matter. This is also one of the best cybersecurity measures for businesses.
- Implementation: Schedule regular training (quarterly or twice a year) using online modules or live workshops. Platforms like KnowBe4 or free resources from CISA work well. Tailor training examples to your industry, and include security in onboarding and employee performance goals.
- Effort/Cost: Low. Many ready-made training modules exist, so costs are modest. The main investment is staff time.
- KPIs
- % employees trained
- phishing test click rate
- number of reported suspicious emails
- time to report incidents by staff
9. Third-Party & Supply-Chain Risk Management
Every vendor, supplier, or partner you work with can be a potential risk. Because if they’re compromised, attackers can reach your systems through them. In fact, supply-chain attacks have risen sharply, and third-party breaches have spiked in recent years.
That’s why evaluating vendor security is crucial. Ask vendors to share their security policies, audit results, and include clear security requirements in contracts such as encryption standards, breach notification timelines, and compliance obligations. Use formal questionnaires or platforms to check their risk level, including cyber hygiene, past incidents, and financial stability.
Monitoring shouldn’t stop after onboarding. Continuously keep an eye on critical partners, and consider things like cyber insurance or joint tabletop exercises with key vendors. Treat their access like you would an employee account: enforce strong IAM controls and remove access as soon as contracts end.
Following these steps is a key part of cybersecurity measures for businesses, and also helps implement network security measures for companies beyond your internal systems.
- Implementation: Keep an up-to-date list of all third parties that handle your data. Request security documentation like SIG questionnaires or audit reports. Use vendor risk management platforms such as Panorays or SecurityScorecard to automate assessments. Enforce least-privilege access via VPNs or accounts, and remove access immediately when a relationship ends.
- Effort/Cost: Medium. Most of this is process and diligence. Some costs may apply if using scoring or assessment services. Larger vendors may also require formal security plans.
- KPIs
- % of critical vendors assessed
- average vendor risk score
- number of third-party incidents
- contract compliance rate
10. Governance, Policies & Compliance
Using tools and technology doesn’t mean security. Security needs to be part of how your business is run. Governance, policies, and compliance help make that happen.
- Start by using a recognized framework, like NIST CSF or ISO 27001 to guide your policies and controls.
- Regular risk assessments like an annual NIST gap analysis that helps identify what matters most. Make sure your business meets all applicable regulations, whether it’s GDPR, HIPAA, CMMC, NIS2, or others.
Document all cybersecurity policies clearly (things like acceptable use, access control, incident response) and update them as threats and regulations change. Leadership involvement is key. Reporting risk metrics to executives or the board helps secure budgets and align priorities across the organization.
This step ties all your cybersecurity measures for businesses together and is considered one of the best cybersecurity practices for businesses because it ensures that security is not just reactive but built into the business culture.
- Implementation: Adopt a standard framework and tailor it to your business. Create written policies covering all measures discussed –passwords, device use, incident handling, and so on. Perform regular internal or external audits. If needed, align with industry-specific standards like PCI DSS for payments or NIST 800-171 for government data.
- Effort/Cost: High. Building and maintaining a mature governance program takes time and effort. Consulting services or compliance tools can help make the process easier.
- KPIs
- framework implementation level (e.g. NIST CSF Tier)
- number of policy violations detected
- findings from audits
- compliance certifications achieved
5-Point Action Checklist
1. Assess Risk: Perform a cybersecurity risk assessment or framework gap analysis to prioritize controls.
2. Enable MFA Everywhere: Immediately turn on multi-factor authentication for critical accounts and VPN logins.
3. Update & Patch: Review software inventory and apply all critical security patches; automate future updates.
4. Back Up & Test: Verify that encrypted backups of all essential data are in place and perform a restore test.
5. Train & Plan: Roll out a quick security awareness session for staff (phishing check) and review your incident response plan.
Final Thoughts on Cybersecurity Measures for Businesses
No single technology can stop every attack; a layered approach is essential. In 2026, businesses need to combine these above mentioned cybersecurity measures to build true resilience. Regularly revisiting and practicing each measure, as recommended by CISA and NIST, ensures your defenses stay strong.
And if your organization relies on custom applications, partnering with a trusted mobile app development company in USA can help integrate security from the start, so your apps don’t become a weak link.
By implementing these top cybersecurity measures for businesses, and with continuous improvements and the right tools, businesses of any size can significantly reduce risk and protect both operations and customers in 2026 and even beyond.
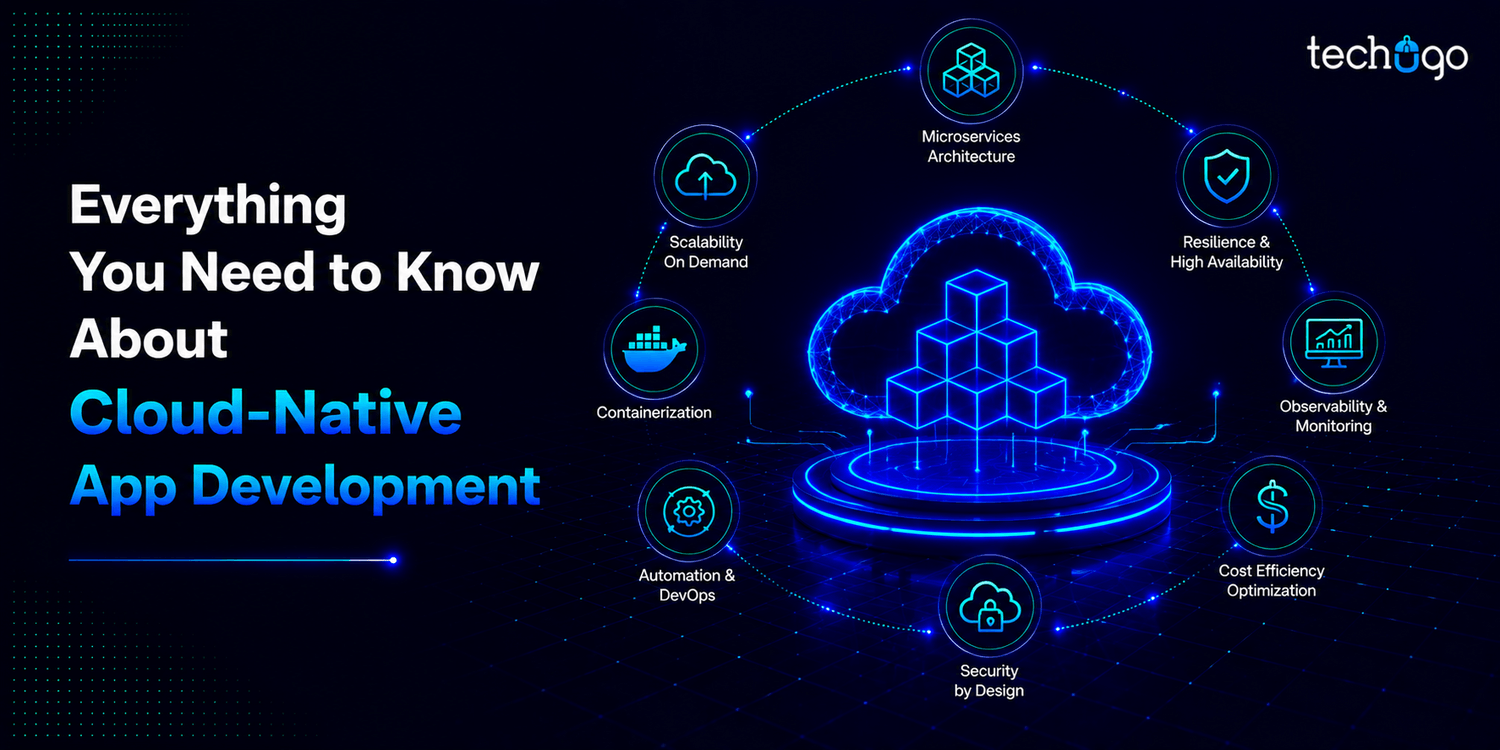
How Techugo Can Strengthen Your Cybersecurity Strategy
Creating digital products that have security incorporated begins with having a proper foundation; as a reliable AI app development company, Techugo has a strong focus on integrating security into all product life cycle phases including: Planning, Design, Development and Deployment.
Regardless if you have a new brand or are simply trying to grow your existing brand, Techugo helps support you in developing applications based upon secure coding best practices, ensuring you meet all required data protection specifications and compliance.
Ultimately, Techugo not only allows you to develop your business; but also helps keep your business safe while you expand. You can reach out to us anytime for any queries.
Get in touch
We'd love to hear from you.



 SA
SA  KW
KW  IE
IE AU
AU UAE
UAE UK
UK USA
USA  CA
CA DE
DE  QA
QA ZA
ZA  BH
BH NL
NL  MU
MU FR
FR